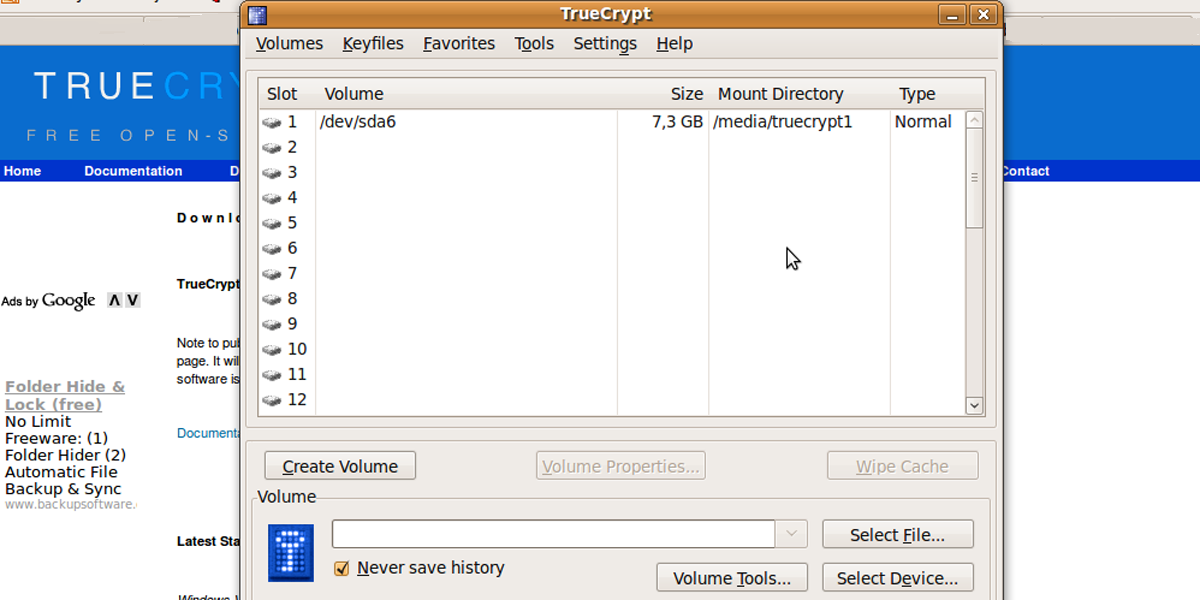
TrueCrypt is one of the standard encryption tools used in eDiscovery to transport data – both coming from source material and in outgoing productions. It’s an incredibly easy-to-use, free, cross-platform tool that presents encrypted “containers” as drives that can be accessed on a local system. On Wednesday, May 28, 2014, the TrueCrypt SourceForge page was updated with an abrupt and ominous warning.
WARNING: Using TrueCrypt is not secure as it may contain unfixed security issues
This page exists only to help migrate existing data encrypted by TrueCrypt.
The development of TrueCrypt was ended in 5/2014 after Microsoft terminated support of Windows XP. Windows 8/7/Vista and later offer integrated support for encrypted disks and virtual disk images. Such integrated support is also available on other platforms (click here for more information). You should migrate any data encrypted by TrueCrypt to encrypted disks or virtual disk images supported on your platform.
Instructions were provided for using Microsoft’s BitLocker encryption, along with a new release of TrueCrypt containing warnings about its insecurity and removing the ability to do anything other than decrypt existing volumes. The new 7.2 release contains warnings substantially similar to the SourceForge page, and it’s cryptographically signed with a good key for the developers. The differences between the 7.1a code and the 7.2 code include the addition of warnings, removal of encryption capabilities and the odd conversion of “U.S.” in several strings to “United States”. Interestingly, they also removed the licensing restriction that required derivative versions to provide reference back to TrueCrypt, almost seeming to invite a fork of the existing codebase, something their earlier licensing strongly attempted to discourage.
Many are currently speculating that this announcement is a “Warrant Canary” designed to alert users that future versions, even if cryptographically signed, could contain intentionally-placed vulnerabilities likely as the result of a forced disclosure of the private TrueCrypt code signing keys. The developers remain anonymous and have been silent since making the changes to the SourceForge page and updating the new version.
At this time, there do not seem to be known exploits for TrueCrypt; concerns over its security are solely based on the information presented by the developers. The end of life for Windows XP does not seem to be a valid reason to cease development, as even the suggested replacements are poor substitutes for the existing functionality. An active audit of the 7.1a codebase is underway and its initial results were promising. Initial reports are that the audit will continue.
BitLocker is not an appropriate solution for eDiscovery file transport. First, it is included as part of only certain versions of Microsoft Windows. Unlike TrueCrypt, it’s not compatible with other operating systems. Its security is also highly questionable – Microsoft clearly explains that in a non-domain environment, copies of the keys necessary to decrypt the container are sent to and stored by Microsoft.
The choice of an encryption tool is not one that should be taken lightly, nor should that decision be rushed. While many are going to urge an immediate change, with what is known about 7.1a at this point, it is likely safe to continue its use for a short period of time until an accepted alternate can be determined.